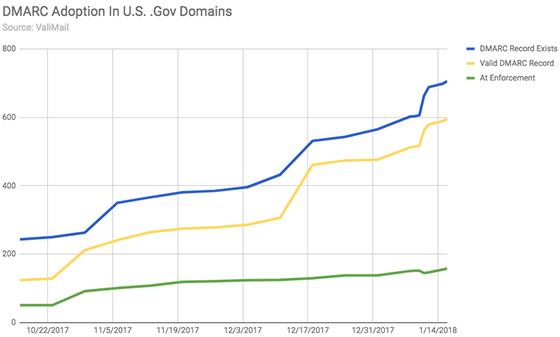
Every federal agency in the United States was directed by the Department of Homeland Security (DHS) to implement email authentication by January 15, but new data from ValiMail reveals that the U.S.
government is still very much at risk of email-based phishing attacks.
The DHS issued a mandate in October requiring federal agencies to have valid SPF and DMARC records within three months,
but only 54.7% of federal domains had a working DMARC record as of Tuesday morning, according to ValiMail.
DMARC, or Domain-based Message Authentication, Reporting &
Conformance, is an email authentication protocol that helps combat email phishing scams. DMARC builds upon the common email validation system SPF, or Sender Policy Framework, to give Email Service
Providers (ESPs) directions on what steps they should take if they discover potentially malicious email that isn’t authenticated.
advertisement
advertisement
For example, brands that have implemented a
“p=reject” DMARC policy have instructed mailbox providers to hold any emails that have failed to pass email authentication measures so that they are not delivered to the inbox. Brands with
a “p=none” DMARC policy have requested to be alerted of any suspicious content, but they have instructed ESPs to deliver the questionable emails regardless.
The DHS mandate
requires all federal agencies to adopt a “p=none” DMARC policy, and just over half have now done this, according to ValiMail. The email security startup, which offers email authentication
as a service, says it has witnessed tremendous growth over the past month as federal agencies rush to implement email authentication. Eighteen domains added DMARC over the 3-day holiday weekend.
Out of the 706 federal domains with a DMARC record, however, only 12% are at an enforcement level. This means that 88% of federal agencies are still vulnerable to impersonation attacks. Although
these domains aren’t necessarily in transgression of the DHS mandate, they are still at risk because suspicious emails are delivered as opposed to being held back.