A day after the Director of National Intelligence Dan
Coats released the U.S. intelligence agencies’ 2018 Worldwide Threat Assessment,
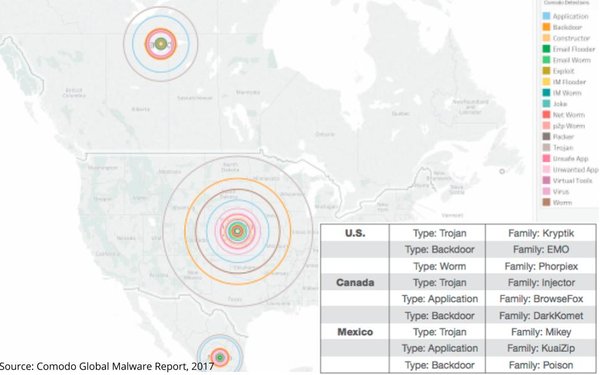
highlighting how digital media has become a vector for a variety of national security threats, a new report revealed the prevalence of malicious code worldwide, as well as in the U.S.
“In the internet era, all major real-world events have a reflection in cyberspace, often in the form of malware, which can be used to steal, block or manipulate data in myriad
unauthorized ways,” reads the Global Malware Report released this morning by cybersecurity company
Comodo.
“While spikes in malware detection at these times could be coincidental, it should no longer come as a surprise when significant events, such as missile launches,
nuclear threats, and other forms of international tension, are reflected in cyberspace in the form of concurrent computer network operations,” it continues.
advertisement
advertisement
The reported noted:
“Elections are a prime example: “In the U.S., on Oct. 24, 2017, Comodo detected a massive spike in Kryptik trojans, totaling to nearly 300,000, over 94% of which were located in the state
of Virginia, where a close and hard-fought gubernatorial election took place.”
While the goals and intentions of malware purveyors are not always clear, the report shows
it’s clearly more than just an economic play to defraud, deny or take control of things for monetary gain.
It also includes a significant efforts to utilize malicious software to
destabilize societies.
“Nuclear activity of any type draws worldwide attention, as nations scramble to gather intelligence and prepare for possible military operations,”
notes Comodo, which is one of the few commercial cybersecurity companies with visibility inside North Korea.
The company said it detected a “startling trojan increase”
occurred in North Korea on September 19, when U.S. President Donald Trump threatened to totally destroy North Korea at the United Nations.
“This prompted deeper
research,” the company said, adding: “Comodo saw not only the top malware types, such as trojan and backdoor, but also a range of uncategorized 'other' malware that helped to provide a
fuller picture, causing spikes in the fall during President Trump’s tour of Japan, South Korea and Beijing and various public statements on North Korea as an accelerating nuclear threat.
“Comodo’s analysis of these detections suggests that North Korean network administrators are attempting to protect computer systems running unlicensed copies of Windows 7, using
a variety of means, including the use of remote access tools to monitor user activity and by trying to bypass Windows User Account Control (UAC).”
So-called “trojan
horse” malware takes its name from Greek mythology and refers to any seemingly useful or benign computer program that has hidden (usually malicious) functionality that can steal, block or
manipulate data on a victim computer.
Cybersecurity experts have known for some time that advertising and digital media buys have emerged as a key vector for distributing malicious
code, especially trojans.
“Attackers use numerous tricks to get users to install a trojan on their computer, from phishing to malicious advertising,” Comodo notes. (See
table below ranking top nations based on trojan penetration.)