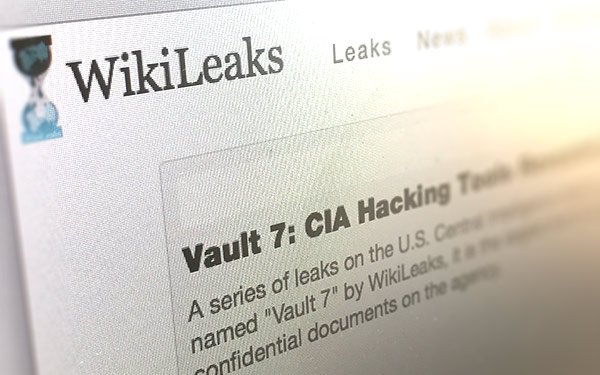
WikiLeaks dumped another batch of classified
documents on Tuesday depicting the CIA’s methods for bypassing encrypted mobile devices and applications.
Dubbed #Vault7, Tuesday’s leak of thousands of Web pages describes the
types of technology the Central Intelligence Agency (CIA) uses to hack targeted citizens and foreign governments. WikiLeaks claims this is the first part of a series of leaks it has titled “Year
Zero,” allegedly taken from the CIA’s Center for Cyber Intelligence unit in Langley, Virginia.
In what may be the largest CIA breach in history, the Vault7 files describe the
software tools the agency uses to break into computers and devices connected to the Internet, including televisions.
The leaked documents also reveal that the CIA has developed sophisticated
technology for hacking Apple and Android mobile devices, collecting audio and messaging data and bypassing encryption on mobile applications like Signal and Whatsapp.
advertisement
advertisement
ProtonMail, an end-to-end
encrypted email service, has confirmed that none of the Vault7 documents indicate the company's encryption has been compromised.
“We can state unequivocally that there is nothing in the
leaked CIA files which indicates any sort of crack of ProtonMail’s encryption,” states Andy Yen, co-founder of ProtonMail, in a blog post. “And despite claims to the contrary, there is also no evidence that Signal/Whatsapp end-to-end encryption has been
breached.”
Founded in 2013 after Edward Snowden’s NSA revelations, ProtonMail has since become a popular and secure email service for journalists, activists, dissidents and privacy
fans.
“Over the past three years, the CIA has put together a formidable arsenal of cyberweapons specially designed to gain surveillance capabilities over end-user devices such as
mobile phones and laptop/desktop computers,” writes Yen. “These advanced malwares enable the CIA to record actions such as keystrokes on a mobile device, allowing them to conduct
surveillance without breaking encryption. Through this technique, US intelligence agencies can gain access to data before they have been encrypted.”
The core
cryptography underlying encrypted services like ProtonMail or What’sApp have not been compromised by intelligence agencies, but the CIA has seemingly disrupted the security of end-user
devices.
“The use of end-to-end encryption means services such as ProtonMail are not actually able to decrypt user data,” writes Yen. “Even if we wanted to compromise
user data, we do not have the technical means to decrypt the user emails. Furthermore, even if an attacker breached ProtonMail servers, all the emails stored on our servers are encrypted,
so an attacker also would not be able to read user emails.”