The U.S.
Department of Justice on Tuesday announced the indictment of two people from Kazakhstan and six Russian nationals for alleged involvement in a digital advertising fraud scheme worth millions.
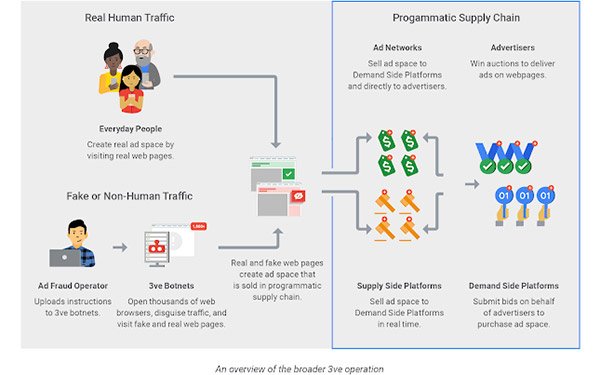
In one scheme that occurred between December 2015 and October 2018, defendants allegedly used malware-infected computers to run automated ad-fraud schemes without users’ knowledge or consent.
The malware hit more than 1.7 million computers and resulted in $29 million in payments for fake digital ads.
advertisement
advertisement
The 13-count indictment was unsealed Tuesday in a Brooklyn federal court as
part of a multi-year investigation into two international cybercriminal rings partly focused on counterfeit ad inventory that led to charges of wire fraud, computer intrusion, aggravated identity
theft and money laundering.
The defendants created more than 250,000 web pages across more than 5,000 domains associated with online publishers, including the domains of thousands of
businesses in the United States and multiple businesses in the Eastern District of New York.
“This case sends a powerful message that this Office, together with our law enforcement
partners, will use all our available resources to target and dismantle these costly schemes and bring their perpetrators to justice, wherever they are,” stated United States Attorney
Richard Donoghue.
The ad fraud operation included more than 3 billion daily bid requests, 1 million compromised IP addresses and 700,000 active infected devices.
In early
2017, Google began seeing indications of a botnet -- nothing surprising or unusual, according to one source. Then it noticed another botnet, which was semi-connected to the first, so Google reached
out to White Ops, a cybersecurity company, to help it sort through the details.
Google turned the information over to law enforcement and involved the Federal Bureau of Investigation (FBI)
after noticing the scale of the operation.
On Tuesday the indictment was announced, along with a published white paper detailing how Google worked with White Ops and the FBI to identify the ad-fraud program and how it worked to protect clients from being
affected.
Since identifying the schemes, Google began pushing the adoption of Ads.txt, which helped to curb the impact to some extent.
In December 2017, Google also changed the way it
handles refunds for invalid traffic with third-party exchanges in Display & Video 360.