Click Fraud Hijacks Bing, Google, Yahoo Searches
- by Laurie Sullivan @lauriesullivan, May 18, 2016
 Malware created to take control of search queries by allowing third parties to manipulate results has affected nearly 1 million machines worldwide -- essentially hijacking
the search.
Malware created to take control of search queries by allowing third parties to manipulate results has affected nearly 1 million machines worldwide -- essentially hijacking
the search.
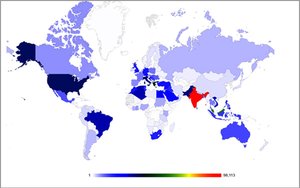
Researchers from Bitdefender released a study this week explaining the click-fraud botnets and highlighting one in particular -- the Redirector.Paco Trojan, which infected more than 900,000 machines worldwide since its release in 2014. The infection rates are heaviest in India.
In searches, the goal of the malware is to help cybercriminals earn money from Google's AdSense program. When the Redirector.Paco malware infects a computer after someone downloads and installs an infected version of Connectify, KMSPico, YouTube Downloader or similar software program, it adds two files -- Adobe Flash Scheduler, and Adobe Flash Update.
Those files activate the malware each time the computer restarts, rerouting the Web traffic through a local proxy server by generating root certificates for the search engines identified by the user's browser. The file tells the browser to redirect the traffic to a different address.
The user queries a search engine and the malware serves up custom search pages with AdSense for Search ads. The thieves earn a portion of the cost-per-click from the AdSense affiliate program each time a user clicks on one of the ads.
One signal of a hijacked search points to a missing distinctive yellow letter "o" in Google, written above the page numbers in the botnet search results that mimic Google's.
The custom search results come directly from the search engines and are made to look authentic, but other more generic clues across the engines that the botnet may affect the computer include slow load times, messages in the browser status bar that read "waiting for proxy tunnel" or "downloading proxy script."



Yep, it's worse than you think. Every type of digital ad is affected by fraud, not just programmatic display and video.
Related: consider the security risks of putting third party JS on your site https://www.linkedin.com/pulse/covert-collection-logins-passwords-mass-surveillance?trk=mp-reader-card
Now more than ever there is a need for a Smart & Simple solution to help advertiser protect themselves as much as possible agianst click frauds, check out our project on clickfrauds.com